Since Winnti (APT41) was sued by the FBI last year, the group has not disappeared. Instead, they have used more innovative and less well noticed techniques to evade detection by security products, such as:
- Avoiding memory detection through dll hollowing technique and one miscellaneous method.
- Using DPAPI to encrypt the real payload to make forensics more difficult.
- Abusing the certificate to hide the payload in a signed PE file.
- Using Cloudflare Worker to hide the real IP address.
- Using legitimate tools like InstallUtil to execute code and bypass application whitelisting.
In addition to malware that is known to be used by Winnti , we also found some newly developed malware. There are two new pieces of listening port malware, RBRAT and a Stone variant. We also found a shellcode-based backdoor, Natwalk, and the method it used to call the Windows API was also innovative, making the reversing more difficult.
The group is also more careful in their usage of C2. They use DNS tunneling extensively as well as Cloudflare Worker to hide their real C2 IP.
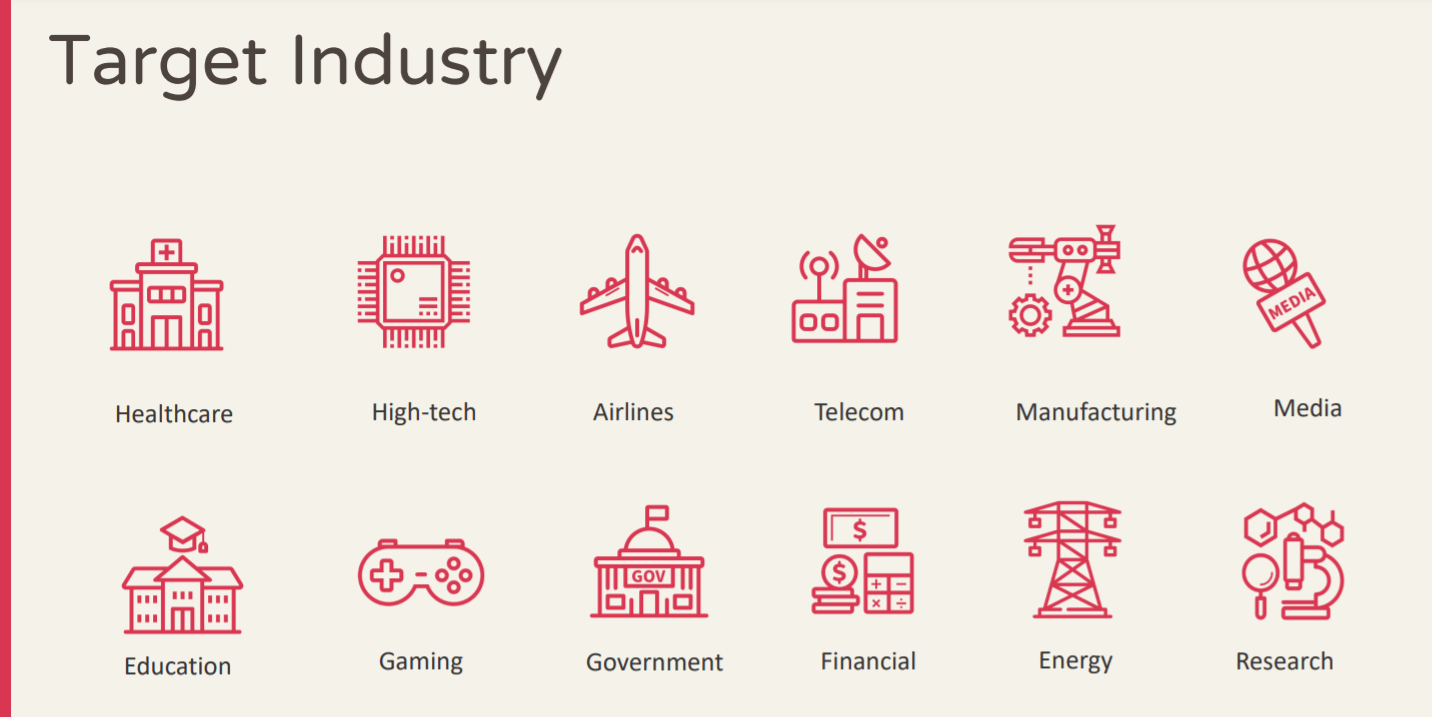
We have observed that Winnti targeted telecommunications companies, key medical institutions, governments, and major infrastructures in various countries in 2021.
The prosecution did not deter them, but instead prompted them to evolve their attack techniques, and make it harder for researchers to track and detect.
In this talk we provide more details about the campaigns of Winnti , including its innovative TTPs, newly developed malware, lateral movement techniques, and the strategies they used for C2 after they were sued by the FBI.
Slides of the talk can be downloaded on the official website : Link