Executive Summary
A critical vulnerability in WinRAR's ZIP file processing has been discovered, enabling attackers to distribute malware, with a focus on the cryptocurrency industry. Users are urged to update to WinRAR version 6.23, as numerous weaponized PoCs have emerged.
CVE-2023-38831 Details
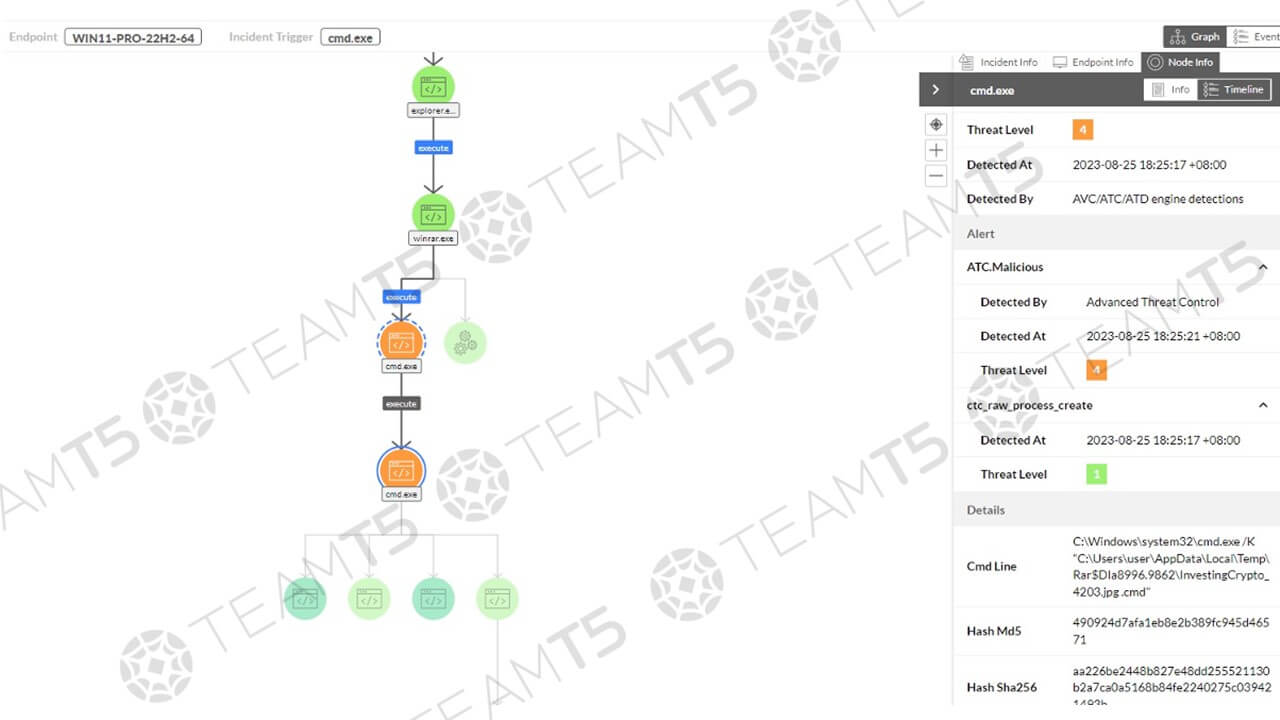
Threat actors can exploit CVE-2023-38831 with a crafted RAR file to deploy malware to the targets’ devices. Such RAR files are created with spoofing extensions, disguising as standard file formats such as .txt and .jpg to lure the target into execution. User interaction is required to exploit the vulnerability, but as users believe they are opening a standard file, user action is easy to prompt, resulting in a wide range of tactics attackers can implement.
WinRar is a highly popular piece of software, having been on the market for 28 years and available in over 50 languages. WinRar claims to have over 500 million users worldwide, and since WinRar does not update automatically, the impact of this vulnerability is very severe.
Till now, CVE-2023-38831 has primarily been used to target the cryptocurrency industry, and a large number of weaponized PoCs have been released making use of the vulnerability.
Protection
Patching
The vulnerability has been resolved in the latest version of WinRAR 6.23. TeamT5 strongly recommends that all WinRar users update to the latest version to protect their systems. For more information, please refer to the official WinRAR announcement.
Detection
We are pleased to report that ThreatSonar Anti-Ransomware, TeamT5’s endpoint detection and response solution can already detect this vulnerability. ThreatSonar Anti-Ransomware users are already equipped to identify and mitigate this threat and need not worry.
Intelligence
For those interested in a detailed analysis, TeamT5’s intelligence platform, ThreatVision will soon release a comprehensive Vulnerability Insights Report (VIR) on CVE-2023-38831. This report will provide in-depth information and insights to help you understand the nature of this vulnerability and how to best protect your systems. Data regarding the CVE-2023-38831 vulnerability can also be found on 2023-Aug-2’s Patch Management Report(PMR).
Learn more about ThreatVision!
Related Post
製品及びサービス
2023.10.16
脆弱性調査とは?
vulnerability research